Most small businesses do not need another complex security platform. They need the next practical step after antivirus, and they need it to fit a budget and a team that does not include a dedicated security analyst.
That is not our opinion. It is what SMBs themselves report when surveyed at scale. CrowdStrike's State of SMB Cybersecurity Survey is a 291-respondent study of companies with fewer than 250 employees, conducted in February and March 2025. It is about a year old now, and nothing in the SMB threat picture has changed since to make the numbers more flattering. The findings line up directly with the brief we built ZeroExfil against, so the rest of this post walks through their numbers and what they imply for what an SMB-appropriate next layer should look like.
Awareness is high, execution is not
The opening finding from the survey is the gap between knowing and doing.
- 94% of SMB leaders say they are knowledgeable about cyber threats.
- 83% have a cybersecurity plan in place.
- Only 42% provide regular employee training.
- Breach rates are statistically identical between companies that have a plan (25%) and those that do not (24%).
That last data point is the one worth sitting with. Having a plan is not protection. The plans exist on paper but are not being executed, because executing them requires either a security team to run the playbook or tooling that does the equivalent work without one. Most SMBs have neither.
The toolset is stuck in the previous decade
The survey asked SMBs which tools they actually use. The answers are honest:
- 91% use commodity firewalls.
- 89% use multifactor authentication.
- 70% use traditional antivirus.
- 11% use AI-powered tools to defend against AI-driven attacks.
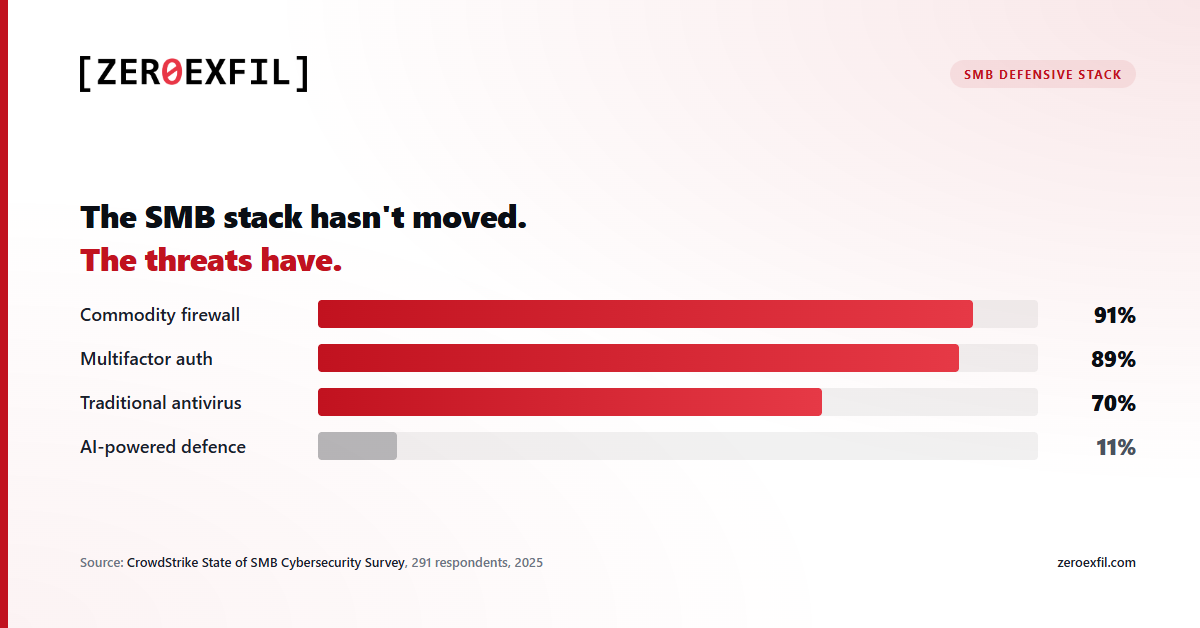
This is the heart of the problem. The threats have shifted toward fileless malware, credential theft, and zero-day exploits, all of which routinely bypass signature-based AV. The defensive baseline at most SMBs has not shifted with them. Not because SMBs are unaware of this, but because the next tier up (EDR, XDR, SIEM, MDR) is priced and shaped for organisations with a security team to operate it.
Cost is the wall
The survey is unambiguous about why the upgrade does not happen.
- 66% of SMBs name cost as the top obstacle to adopting more advanced security tools.
- 67% say cost is the leading factor when choosing a tool.
- Only 57% say protection against advanced threats is a leading factor.
- Only 7% describe their security budget as "definitely sufficient".
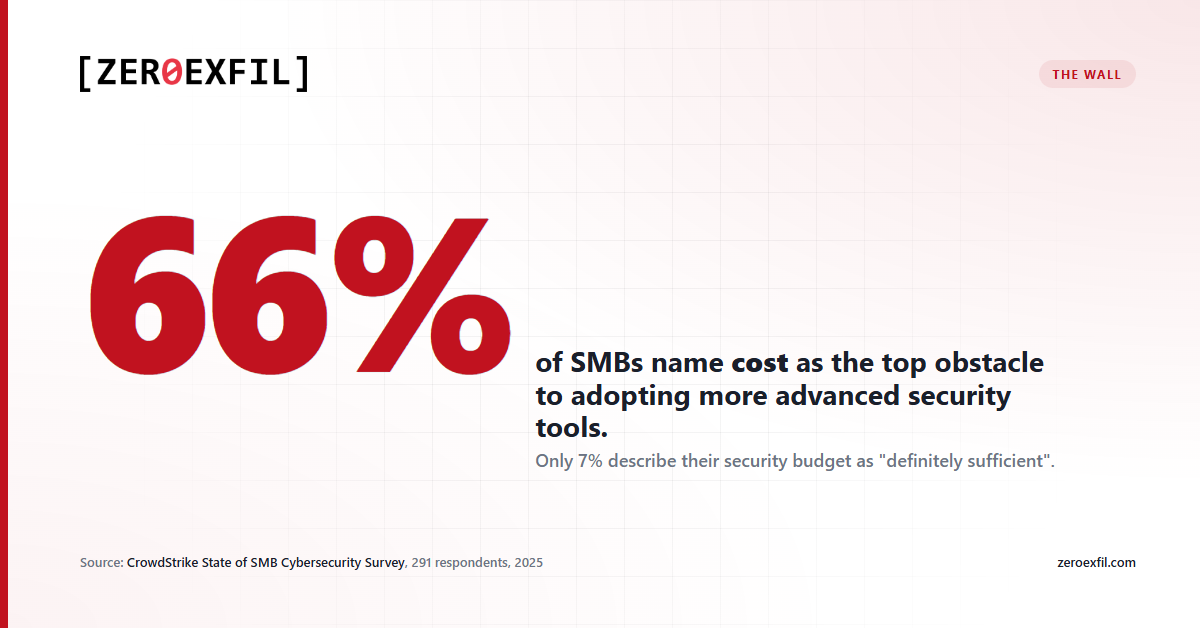
When cost outranks effectiveness as a buying criterion, you end up with the stack the previous section described: cheap, familiar, signature-based, and out of step with the threats that actually land. Vendors who only sell at enterprise pricing have priced themselves out of the segment, and the segment has stopped shopping above antivirus.
There is no security team to operate complex tooling
Even when budget is found, the operating model breaks down.
- 70% of SMBs rely on general IT staff for security work.
- 21% outsource it to a managed provider.
- 50% say they feel overwhelmed by the number of security tools and choices on the market.
- 70% turn to outside experts when selecting tools.
Translation: the buyer is a generalist. The operator is a generalist. Anything that requires a dedicated analyst to triage alerts, write detection rules, or manage policy at scale is not going to be operated. It will be installed, ignored, then quietly cancelled at renewal.
The implication for any tool aimed at this segment is concrete. It has to look and behave like the SaaS the rest of the business already uses. It has to default to useful out of the box. It has to either auto-respond or generate plain-language alerts a generalist can act on. Anything else gets shelved.
The smallest businesses get hit the hardest
The survey's most uncomfortable finding is about the smallest companies, the ones least equipped to recover.
- Among SMBs with fewer than 25 employees that suffered a cyber incident, 29% reported a ransomware attack. For larger SMBs (150-249 employees) the figure was 19%.
- Only 14% of SMBs with fewer than 51 employees rank ransomware as their greatest concern, compared to 24% at larger SMBs.
- 75% of micro-businesses say a major cyberattack would "likely" or "definitely" put them out of business.

The gap between perceived and actual risk for the smallest businesses is the worst possible combination: high impact, low awareness, and no fallback. Antivirus alone catches a portion of these incidents but misses the part that hurts most, which is the credential theft and file-level activity that precedes the ransomware payload itself.
What belongs in the gap
Synthesising the survey, an SMB-appropriate "next step after antivirus" has to satisfy a fairly specific brief:
- Affordable enough to clear the cost objection. Cost is the number one obstacle. Pricing has to be flat, predictable, and small enough that 66% of buyers stop saying "we cannot afford it".
- Operable by a generalist. No SOC, no detection engineer, no separate query language to learn. Defaults that work, alerts a generalist understands, and either auto-response or one-click response.
- Aimed at what AV misses. The threats causing actual damage are credential theft, ransomware-style file behaviour, and document staging or exfiltration. A second layer needs to watch those specifically, not duplicate signature scanning.
- Lightweight on the existing stack. SMBs already have AV and a firewall. The new layer should sit on top, not replace, and not require ripping anything out.
Where ZeroExfil fits
That brief is the one we built ZeroExfil to satisfy. Concretely:
- We watch every file read, write, rename, and delete at the kernel level. Ransomware-style behaviour, infostealer access to saved credentials, and archive-staging patterns light up the same way regardless of which process or runtime is responsible.
- The agent ships with detections for those behaviours out of the box. A generalist IT admin does not need to write a rule to catch a credential sweep or a mass-encrypt event.
- Response actions can run automatically, so a ransomware-shaped event does not have to wait for a human to triage it at 2am.
- Pricing is flat at $5 per endpoint per month. No tiers, no per-feature unlocks, no minimum seat counts.
- It runs alongside Defender or any other AV. We are the second layer, not the replacement.
None of this is exotic. It is what the survey says SMBs need: file-level protection that catches what AV misses, runs without a SOC, and is priced to be bought.
The takeaway
Antivirus is the floor. A full SOC, with EDR, SIEM, MDR, and a team to run them, is out of reach for the businesses that the threat data says are getting hit hardest. The middle layer has been missing for years, which is why CrowdStrike's findings are not a surprise. It is also the gap the rest of the security industry should be building for, not against.
If you run an SMB and you have antivirus but nothing past it, the survey is a useful mirror. The threats your AV is missing are the ones in the news every week. The reason you do not have anything watching for them is almost certainly cost or complexity, not unwillingness. That problem is solvable, and it does not require an enterprise-grade contract or an in-house analyst.
