The next step after antivirus
Antivirus stops known malware. ZeroExfil stops what comes next.
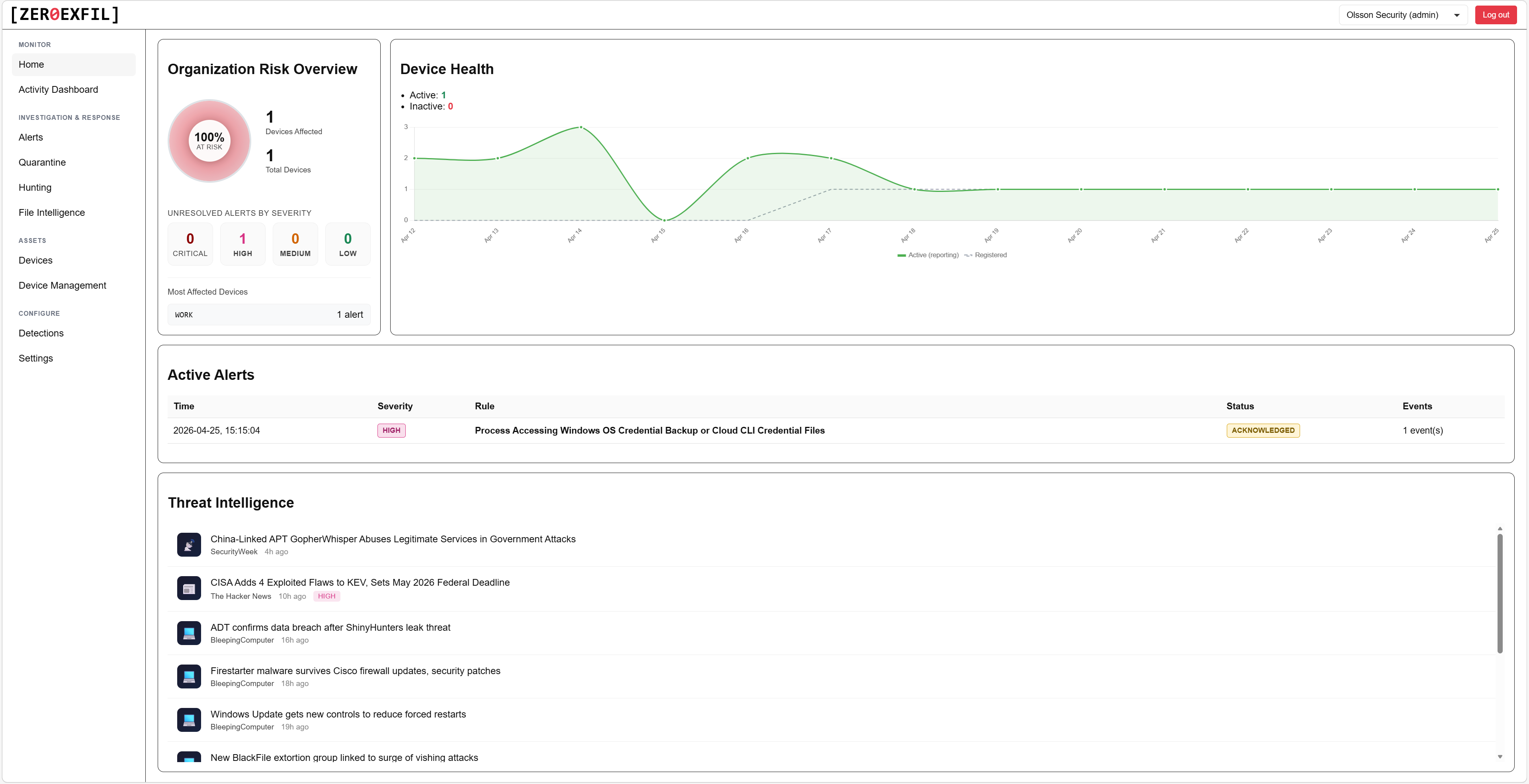
When ransomware, info stealers, compromised users, or rogue tools start reading, staging, encrypting, deleting, or moving files, ZeroExfil detects the behavior and helps you respond automatically. Built for small and midsize businesses that need more than antivirus without running a full SOC.
$5 per endpoint per month. No SOC required. No log-volume surprises.
Keep your antivirus. Add the next layer on top.
Your AV is doing its job: blocking the malware it knows about. ZeroExfil sits alongside it and watches what happens to your files, so the threats that slip past signatures, ransomware behavior, info stealers, and quiet exfiltration, do not go unseen.
What your AV already covers
- Blocks known malware and suspicious binaries
- Scans files on write and on execute
- Quarantines threats it can identify
- Reports on what it blocked
What ZeroExfil adds on top
- Detects suspicious file behavior, even when nothing matches a signature
- Captures reads, writes, renames, and deletes across every file type, in real time
- Correlates each event with the process, user, and bytes transferred
- Responds automatically: isolate the endpoint, kill the process
AV tells you whether known malware was blocked. ZeroExfil tells you what is happening to your files: read, staged, encrypted, deleted, or stolen.
The threats SMBs actually fear
Not generic "advanced threats". The events that cost real money: ransomware, file theft, info stealers, and compromised users.
Monday morning, every file is encrypted
Payroll, contracts, customer data, all locked. The attacker wants six figures and your backups are three weeks old. ZeroExfil catches the encryption pattern within seconds and isolates the endpoint before it spreads to the file server.
An attacker logs in as your finance manager
One bad click and the saved logins for your bank, accounting system, and Microsoft 365 are scraped and sold. The next wire transfer goes to the attacker, and the invoices your customers receive are theirs too. ZeroExfil catches the credential theft and quarantines the process before it leaves the endpoint.
Your customer list walks out the door
A process sweeps user folders, packs documents into an archive, and prepares to upload. By the time anyone notices, the data is already with a competitor or on a leak site. ZeroExfil correlates the read sweep with the archive creation and surfaces the process, files, and bytes involved.
Someone read the files. You have no idea who
A compromised account, a leaving employee, or an AI coding assistant can quietly read anything the user can. Without a record, you cannot prove what was taken. ZeroExfil logs every file event with the process and account behind it, so you always have an answer.
Built for the company without a SOC
A full EDR / MDR / SOC stack is expensive and operationally heavy. ZeroExfil is the practical layer in between.
No analysts required
Our built-in AI investigator (CORA) performs the first round of analysis on every alert. High-confidence false positives close automatically. You only see what matters.
No SIEM required
Telemetry is captured, stored, and queried in the ZeroExfil portal. No log forwarders, no ingest contracts, no surprise volume bills.
Roughly 1 day of IT effort per 200 endpoints
A standard Windows MSI. Deploy with Intune, Group Policy, or your RMM. Agents register automatically and start protecting right away.
Complementary, not a replacement
ZeroExfil closes the file-visibility gap in your existing endpoint security. Keep your antivirus or Defender. Add the layer that catches behavior, not just signatures.
One published price
$5 per endpoint per month. All detections, CORA, automated response, and hunting included. No per-incident fees, no separate SOC fee.
EU and Swiss data residency
Your file telemetry stays in region. Multi-tenant ready for MSPs and multi-site teams.
Try the next layer of defense. Free for two weeks.
Two weeks, up to 10 endpoints, free. We provision your tenant within an hour, walk you through deployment, and run a live detection with you. You see ransomware-like activity, suspicious file reads, and archive and staging behavior directly in the portal. No card, no commitment, no auto-conversion.
Prefer email? Reach us at contact@zeroexfil.com
